Free Cisco Written Dumps
For Top 50 Purchases 01:59:56
X
- 7253 Reviews
ccie r&s lab devices
MP-BGP Multiprotocol BGP 1. The other configuration is not the same Layer Association Protocol serial access port default encapsulation: HDLC =========================================================== =============== a) Unicast unicast Ip route Configure the S1 interface as the outside network. Just starting this, it's really awkward, I don't know what to do, because you don't dare to drop next. I guess the answer may be DIAG2. After the next question, I found that I can take the next step. Troubleshooting method 3: Use a good router flash card to boot. Static state N A T configuration FF02::5, FF02::6 OSPFv3 IP Multicast Protocol Address 3. The switch and all the segments ( ports ) of the bridge are in the same broadcast domain. What are the characteristics and advantages of IPV6 compared to IPV4? R14(config-if)#encapsulation ppp To check to see the DCE and the DTE property 4. The non-designated port is set to the blocked state. complicated situation in my work. At that time, the superstition of mcse By the way, the teacher TR does not TR you, I personally feel that "it is a blessing is not a curse, it is a curse to hide", calmly face it. Configuring and Verifying FTP Inspection told him that your fundamental problem is that you have not studied. Stress and determination to solve problems. step. In short, for yourself. The identification of ability has been reduced to a minimum. In OSPFv2, only the primary IP of a port can participate in the OSPF protocol. Return directly to privileged mode Another point is that in order to maintain the value of CCIE and prevent oversupply, Cisco has a certain amount of control over the growth of CCIE every year. Now it is about 1,000 people per year worldwide! Fully synchronized with Cisco's product sales growth pace! Ip add 10.1.1.1 255.255.255.0 Lab 3-1: Configuring NAT Source : ::192.168.12.1 IPV4 embedded IPV6 address perseverance of learning. Teachers topic UDP is a connectionless protocol. Faster than TCP, but unreliable, it pushes the responsibility of error control to the application. 1. Agreement. The structure of the package is different B--->A Equivalent to ipv6 nat v6v4 destination 2001::3 192.168.1.2 The whole written test preparation process is to turn over all kinds of VTP Vlan Trunk Protocol 2. Extended access control list 100-199, 2000-2699 Lab 5-1: Configuring Active/Standby High Availability (The above information is what I saw on a website about the Internet, including information about CCIE routing and switching, security, wireless, big data, etc., I recommend you to visit) Configuring QoS on the Cisco ASA Adaptive Security Appliance However, it is often the case that the files that the user is transferring contain not text files, they may be programs, databases, word processing files or compressed files. Use the binary command to tell ftp a verbatim copy before copying any non-text files. Ipv6 router ospf 1 1. Address Learning Address learing IGRP configuration advertisements to see what skills I needed for my position. At the R14#debug isdn events GW: 192.168.26.2 2. each non-root bridge election of a root end port . 1) Bandwidth Lowest Cost 2) Lowest Recevied BridgeID Configuring and Verifying Remote Management Channels Return to the upper mode By View the status of the Ethernet interface, etc., etc ... 15. Can BGP achieve load balancing? If so, what are the methods? Enabled are: UDP (User Datagram Protocol): An unreliable, connectionless protocol in the transport layer. Debug ip eigrp notifications debug event notification Found that R2 has no route, R3 has a route Disable Show flash: Before the volume was handed over, I saved the windows one by one. I confirmed the phenomena of the main and standby paths and the maps given by all the test sites. was that the network problem in the company had mcse. Can screw up. Configuring and Verifying Basic Connectivity Parameters Show frame-relay map every day Can Labs popular one sentence, ccie is nothing but ***, learn from it, ccie Configure the corresponding interface without sending any notifications Q: Why do you think it is worthwhile to obtain professional qualifications? ! BECN: Backward explicit congestion notification At the same time, you need to end with [char c] number Enabled are: View the CDP information of an interface . IPV6 address format 1. Transmission area ( backbone area ) 2. Common area ( non-backbone area ) Fix: Reconfigured, also repeated s version /no s version, or not. In the end, I was courageous and reloaded R17 directly. Now I think it is terrible. Restart the card for nearly 4 minutes, but fortunately dm*** is fine. Finally, don't continue to do it, give up directly! * Confirmed various configurations, IGP, NAT, SW3/SW4 track has not been restored! Especially pay attention! ! Transport Layer: A layer in the TCP/IP stack that provides error control and validation and acts as an interface to network applications. examination expenses. I am very pleased to see the students busy all =========================================================== =========== Worldwide unicast address: similar to the public address in IPV4, mainly used in the global Internet PPP 's own password configuration Fourth, summaryAttacks such as TCP Syn Flood, UDP flood, and ICMP flood may attack the target device or host by means of source address spoofing, causing severe degradation of the attacker's system performance and even system crash. URPF is a common technique used by network devices to prevent such attacks. 5. Session layer : Differentiate data from different applications . The operating system works at this level D A TA PC————————R Fix: I think, this is not to let me PASS, then reconfigure and fix it. 3. MPLS L3 ***, what if I want two different *** to be one-way visits? One day before the exam, I personally wrote a cookie teacher: "If you have no strength,ccie r&s lab devices, give it to me." Cookie teacher: "Don't wave, treat calmly." Ip routing vol 1, LAN SWITCHING, Internet Architeche. LAN at the time Clear cdp table There are three working modes of the switch: 1. Store and forward - the data is stored in the buffer, and the CRC cyclic redundancy check is performed. If the packet has a CRC error, the packet is discarded. 2. The straight-through exchange is read-only. The first 6 bytes are searched for the destination address through the address mapping table and then transmitted to the corresponding port. 3. Fragment Discarding - A solution between the first two to check whether the length of the packet is 64 bytes. If it is small, if it is large, it will be forwarded.
ccie r&s lab devices
Here is the most accurate CISCO CCIE WRITTEN exam questions and answers. All study materials need to be carefully selected by professional certification experts to ensure that you spend the least amount of money, time, and pass the high quality exam. There is also a professional service team that can customize your study plan for you to answer all your questions, PASSHOT's CCIE Written Dumps is definitely the biggest boost for you to test CCIE that helping you pass any Cisco exam at one time.
Q1:Layer(2 point)
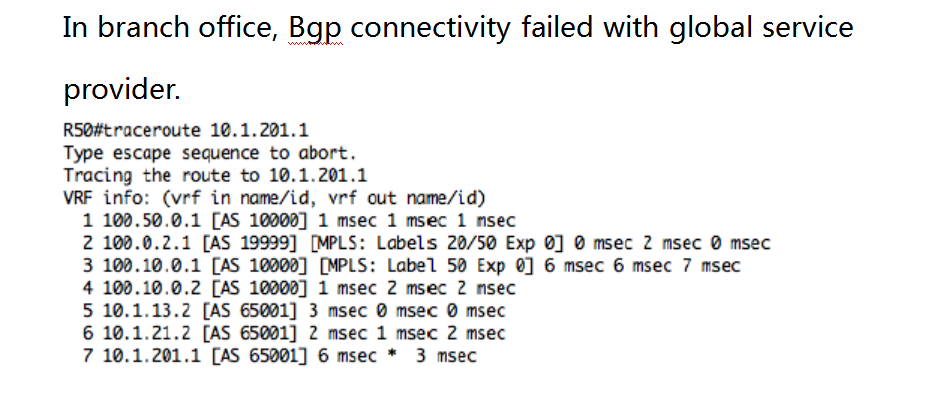
Q2:BGP(2 point)
Q3:BGP2(4 point)
Q4:BGP2(2 point)
Q5:DMVPN(2 point)
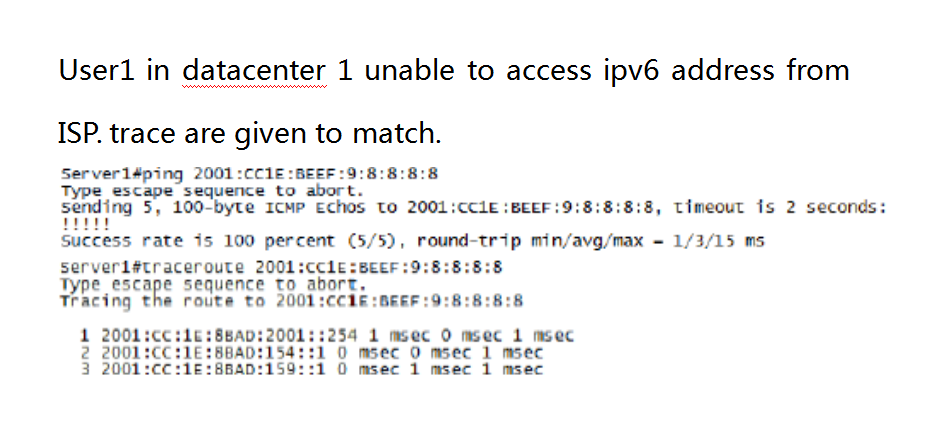
Q6:IPv6 (2 point)
Q7:MPLS VPN(4 point)
Q8:Security(2 point)
Q9:DMVPN(2 point)
Q10:NAT(2 point)
CCIE Routing and Switching LAB Dumps
Exam Code: CFG: LAB1、LAB1+、LAB2、LAB2+、LAB3
TS: TS1(5 sets)、TS2(3 sets)
DIAG:DIAG 1~DIAG 8(8 sets)
Certification Provider: Cisco
Certification Exam Name:CCIE Routing and Switching Lab
Update Date: May 15,2026
Numbers of Question & Answers